Your Website Could Be Vulnerable Right Now
Watch Your Third-Party Scripts
Third-party scripts power your store — from payment systems to chat to analytics. But they’re also prime targets for attackers.
Catch Magecart Attacks Before They Strike
Web skimming attacks silently steal customer card data using compromised scripts. You may never notice – but your customers will.
Understand the Real Risks
A single breach can mean fines, lost revenue and damage to your brand. PCI DSS v4 (2025) now mandates script monitoring.
Want to learn more about Magecart-style threats? Find out more
Detect and Stop Web-Skimming Attacks in Minutes
CartShark continuously monitors your website for suspicious activity, even during live customer sessions. No setup headaches, no slowdowns, no guesswork.
Stop Threats Instantly
Live monitoring spots and flags new suspicious scripts in real time.
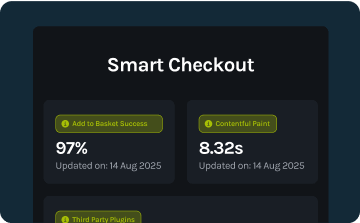
Smart Checkout Simulations
We mimic real users to detect hidden malware where it matters most.
Always Updated Threat Database
You’re protected by the latest AI-enhanced intelligence on known attack vectors and bad actors.
PCI DSS 4.0 Ready
Stay compliant with the latest security standards — effortlessly.
One Platform, Total Visibility
CartShark protects your storefront with a multi-pronged defence strategy.
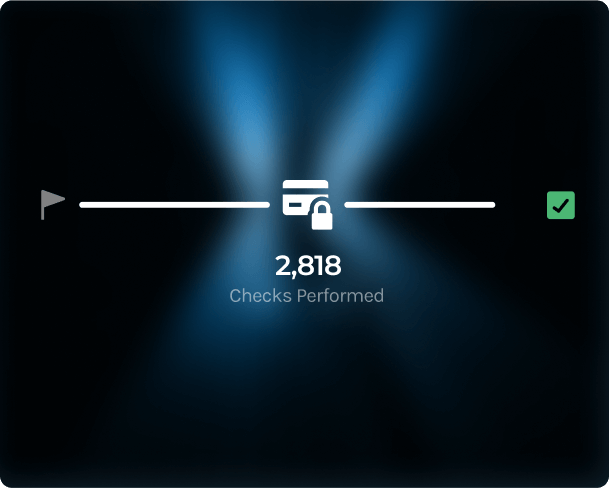
Automated Checkout Monitoring
Simulates real customer behaviour across your checkout flow.
Builds a baseline and flags anything suspicious — instantly.
Proactively spot hidden vulnerabilities and uncover malicious web-skimming scripts.
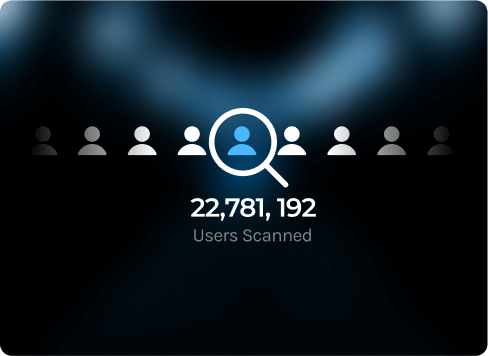
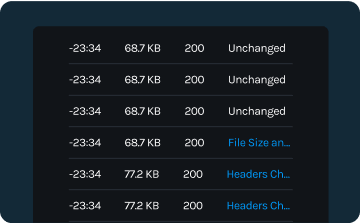
Live User Monitoring
Catch unauthorised scripts lurking beneath the surface by analysing real customer interactions.
Gain actionable insights, identify unusual patterns and nip potential threats in the bud before they cause damage.
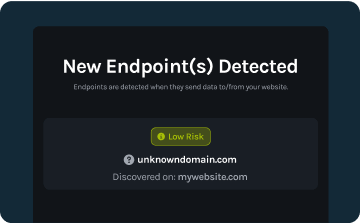
If a malicious destination is added to your website, CartShark will alert you.
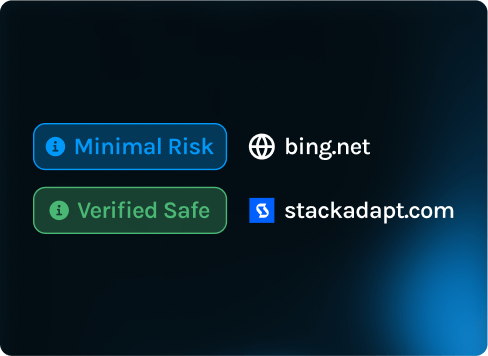
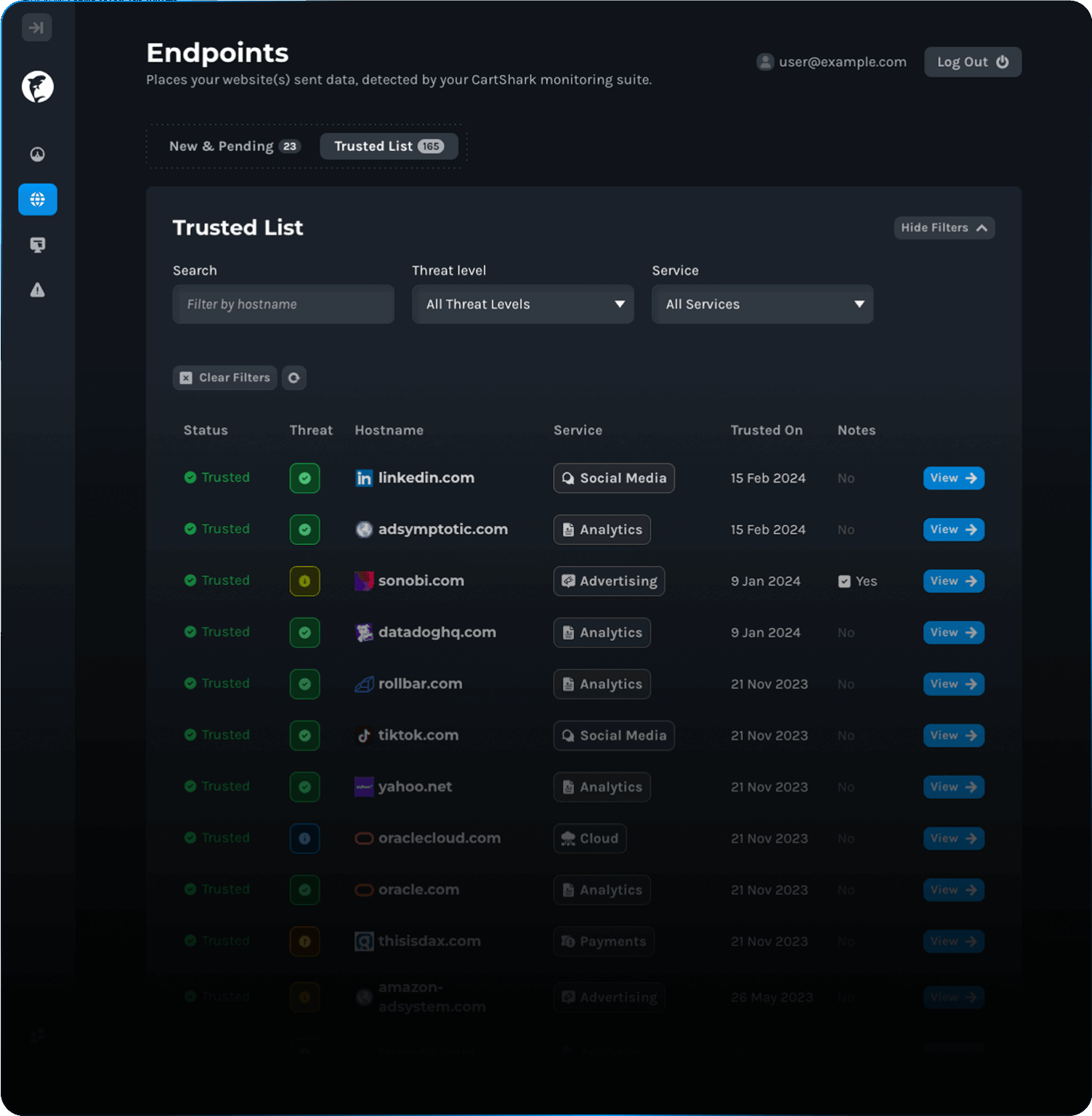
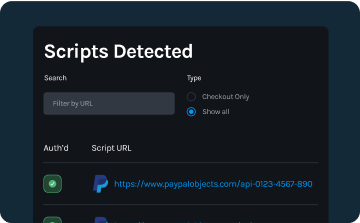
Third Party Tag Management
Automatically tracks and categorises all third-party scripts on your site.
Spot risky vendors before they become a liability.
Don’t let your site become a feeding frenzy for attackers.
Why CartShark?
We’re not another enterprise security tool wrapped in jargon and locked behind a sales funnel. CartShark is fast, fair, and purpose-built for busy online retailers.
“The tool provides full visibility of all data sources across each of our websites – a problem we previously needed to solve.“
Caleb Whittington / Security Engineer, Kurt Geiger

The Answers to Your Questions
Complete Protection for Your eCommerce Business