Protect Your Business and Your Customers
Great reputations are hard to win but easy to lose. RapidSpike can protect you from web skimming attacks, scan for the latest vulnerabilities, check your external perimeter and more.
Security Monitoring:
Protect customer transactions and find out immediately if a data breach occurs.
Track all data sent by third party plugins and receive alerts if they are breached.
Monitor headers, SSL Certs and ciphers as well as other key security metrics.
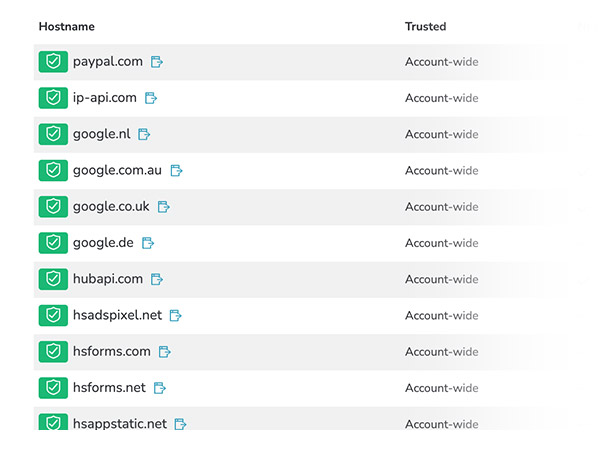
Stop Web Skimming Attacks Fast
The greatest threat to online consumers today is website data skimming.
Often grouped under the term “Magecart”, hackers using web skimming methods are regularly hitting the headlines. RapidSpike attack detection is proven to detect Magecart breaches as soon as they happen.
Manage a trusted list with RapidSpike, monitor every outbound destination and reduce detection time from days to minutes.
Protect your payments
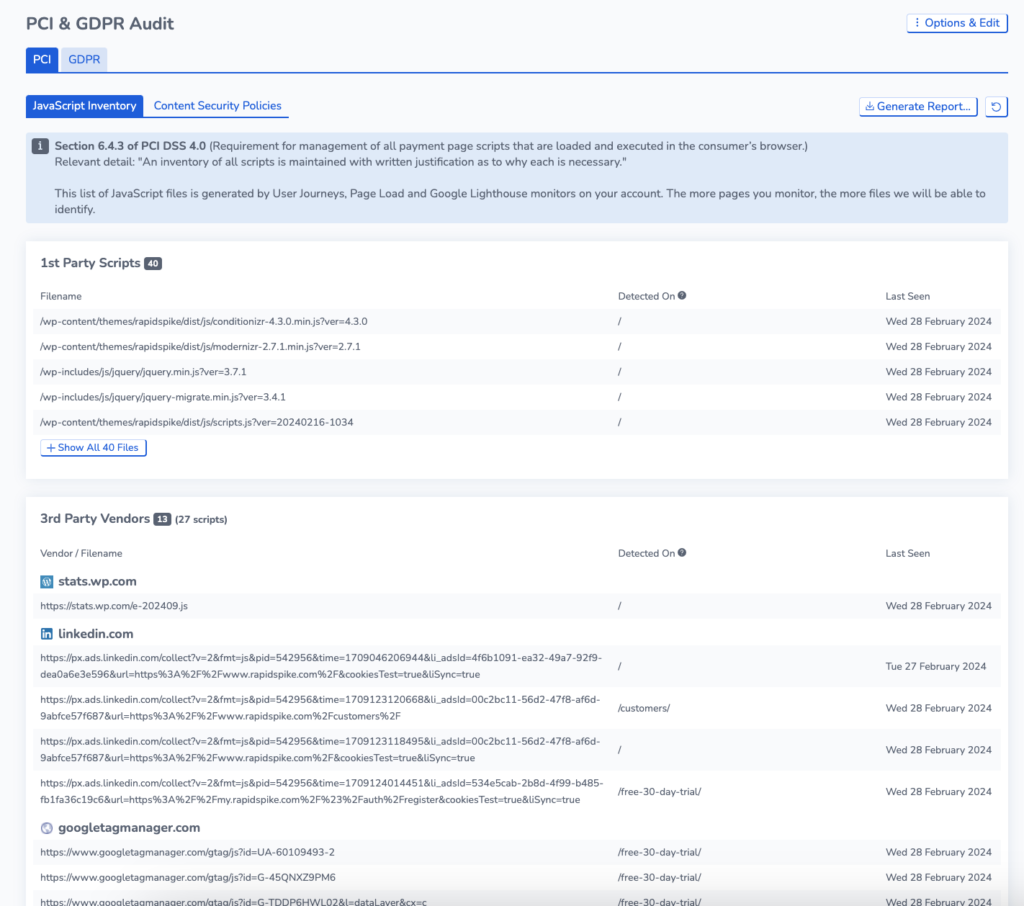
Support your PCI Compliance with RapidSpike and keep an inventory of all scripts on your page.
PCI DSS 4.0 requires website owners to manage all payment page scripts that are loaded and executed in the consumer’s browser.
RapidSpike’s PCI reporting tool provides an in-depth script inventory of all the scripts our monitors encounter on your website.
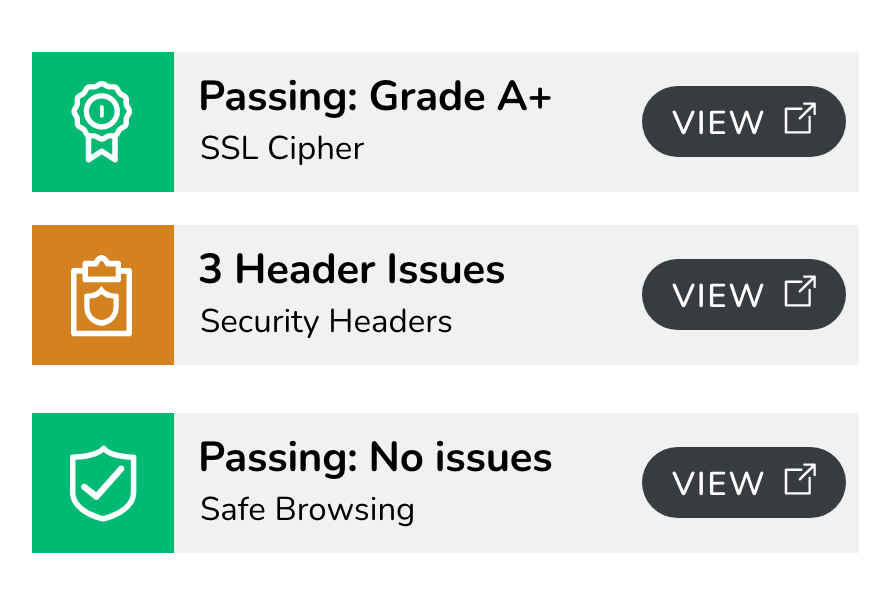
A Watchful Eye on Your Security Perimeter
Protect your infrastructure along a wide range of different security vectors.
Check SSL Certificates, SSL Cipher Score, Security Headers and more. Ensure your external facing systems are not advertising any services that they should not.
Get alerted immediately if something in the perimeter of your network changes.
Insights Into Your Security Data
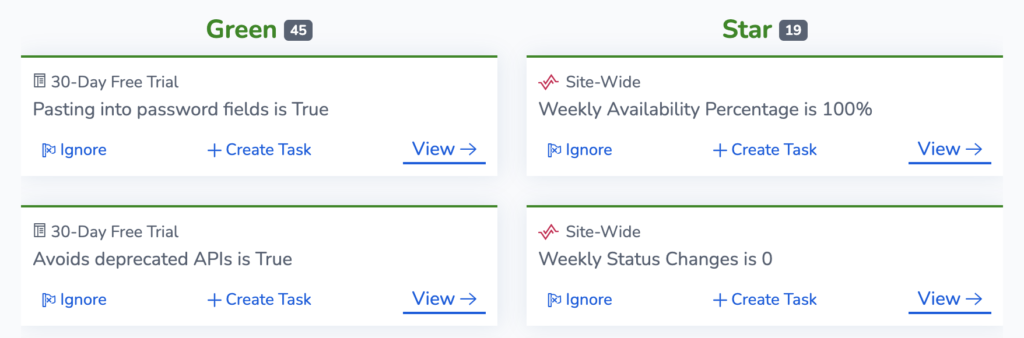
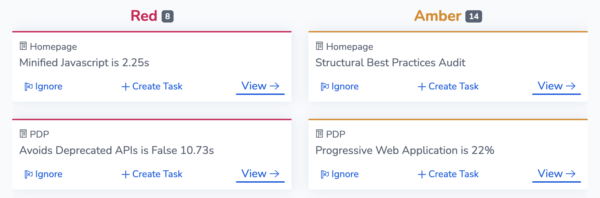
Insights is an intelligence engine that processes your data and produces clear
actionable tasks for you to work on, organised by urgency.
Understand and Prioritise what to fix
Clear actions to support your security perimeter, protect your customers.
Celebrate when you are winning
Tick off areas where your security management excels, and report on your successes.